Your Machines Outnumber Your People. Who’s Securing Them?
Non-human identities outnumber your employees 45 to 1. Cydenti finds and secures them all — in 27 minutes, with zero agents. Hosted in Europe.
No commitment • Hosted in Europe • First report within 3 hours
Adopted by French SMBs and mid-market teams — Connected to 18+ SaaS applications via read-only API
NIS2 Enforcement Begins October 1, 2026. Is Your Identity Governance Ready?
15,000+ French entities are in scope. ANSSI’s ReCyF framework (Objective 13) mandates identity and access governance — covering service accounts, machine credentials, and privileged access. 68% of organizations say they cannot meet initial compliance deadlines.
“28% of security incidents stem from account and permission management failures.”
— CESIN Barometer 2026 (OpinionWay, January 2026)
Total Visibility.
Intelligent Defense.
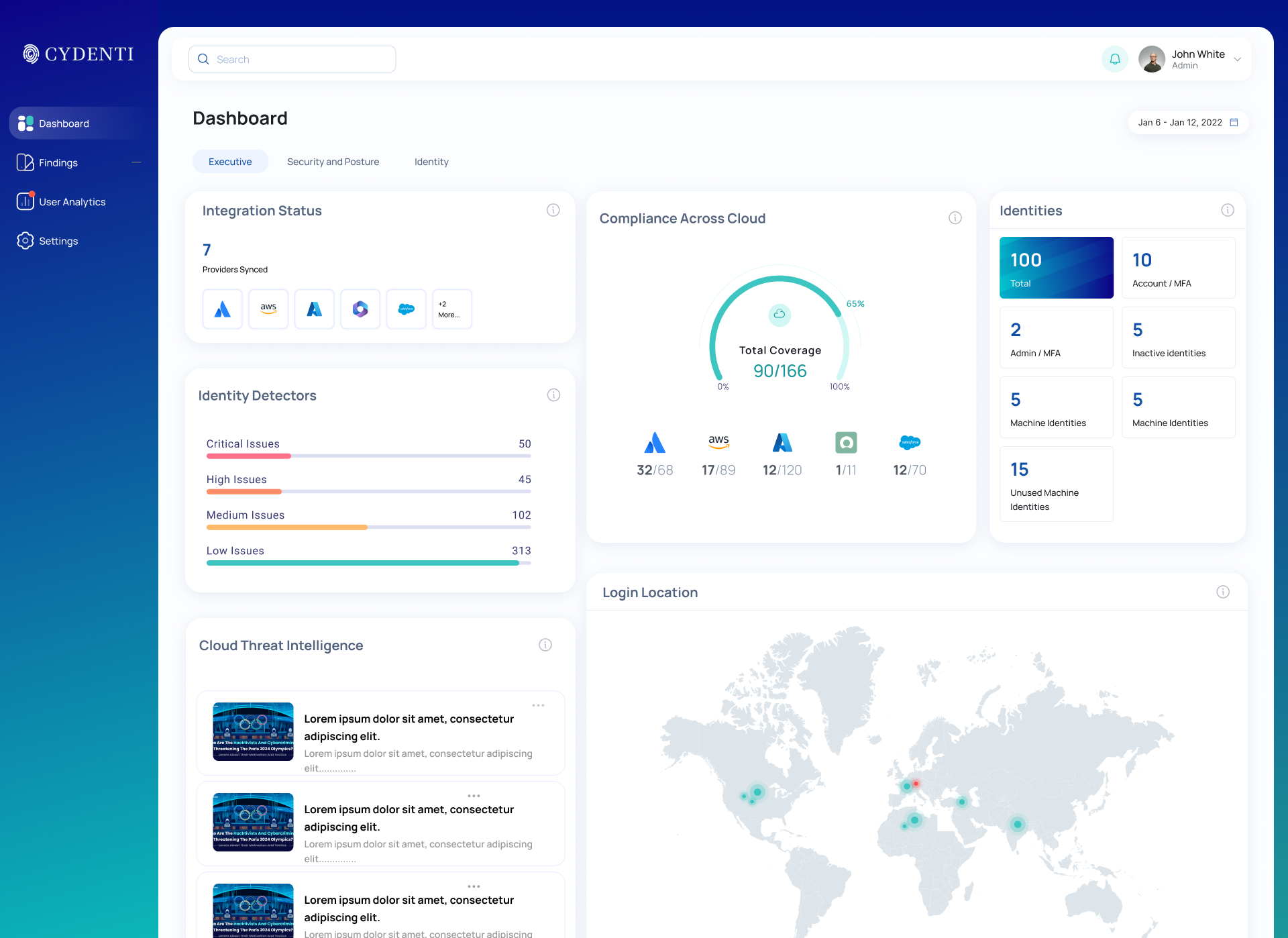
Secure your entire identity fabric—human, machine, and AI—with one unified platform.
ISPM
Identity Security Posture Management
Continuous posture assessment for every identity — human and machine — across your entire SaaS stack.
- Detect drift, over-permissions, and dormant accounts
- NIS2, DORA, GDPR, ISO 27001, SOC 2 alignment
- Prioritized remediation with full context
ITDR
Identity Threat Detection & Response
Detect compromised credentials, hijacked service accounts, and abused tokens — before the damage spreads.
NHI & AI Governance
Non-Human Identity & AI Agent Control
Every AI agent, automation bot, and OAuth integration is a non-human identity with access to your data. Govern them all.
- Full NHI inventory: service accounts, API keys, AI agents
- Control data flows to AI models and third-party apps
- EU AI Act, NIS2, DORA compliance evidence
Most of your team’s work happens on SaaS.
Who’s really watching?
Ghost Accounts
A former employee left 3 months ago and still has access to your Salesforce CRM. An intern inherited admin rights that nobody noticed. 28% of security incidents trace back to account and permission management failures — CESIN Barometer 2026.
Compliance Gaps You Don’t Know About
NIS2 Article 21 requires continuous access control evidence, not last quarter’s screenshots. DORA applies to financial services. Most organizations still lack a structured compliance roadmap for identity governance.
Shadow SaaS Connections
Your SaaS tools interconnect via APIs and OAuth tokens. Salesforce talks to Slack, which talks to GitHub. Every connection is a potential attack surface. Who authorized what, and when?
Non-Human Identities (NHIs)
Non-human identities (NHIs) — service accounts, API keys, OAuth tokens, and machine credentials. For every employee, there are ~20 non-human accounts. Most are unmonitored, over-privileged, and never deprovisioned.
Prevention, detection, and AI governance
— one platform.
The first European platform covering the complete SaaS identity security lifecycle.
Operational in 27 minutes. Not 30 days.
Connect your apps via read-only API. No agent to install. No code to modify. No disruption to your environment.
SaaS Apps
OAuth Apps
Identity Provider
Normalization
Posture Analysis
Identity Graph
Real-time Context
Detection Logic
Risk Engine
AI & LLMs That Actually
Understand Identity.
Cydenti uses in-house LLMs and AI agents to read identity behavior, SaaS posture, cloud permissions, and risky integrations — privately and securely.
- Spots configuration drift instantly
- Flags anomalies in behavior
- Reveals hidden access paths
Automation That
Removes Complexity.
Risk scoring, configuration checks, permission mapping, alert enrichment, and audit reporting — all automated.
Stop Threats That
Others Miss.
Cydenti observes authentication events, applies behavioral analytics, and flags anomalies in real-time. From credential stuffing to MFA fatigue, stop attacks before they become incidents.
User "jdoe" denied 15 push notifications in 2 minutes.
Logins from NY and Tokyo within 1 hour.
Access Explorer
Visualize every connection, permission, and identity path in real-time.
Discover
Ingest identity signals & build the graph
Assess
Score risk & map hidden paths
Remediate
Fix permissions & guide owners
Monitor
Continuous drift detection
Concrete, measurable results
“28% of incidents stem from account and permission management failures.”
— CESIN Barometer 2026 (OpinionWay survey, 397 French CISOs)
Understanding
Blast Radius.
Blast radius is the total potential damage a compromised identity can cause. It's not just about what they should access, but everything they can access through hidden paths, group inheritance, and role assumption.
Mini Case Study: The "Luca" Scenario
Luca is a summer intern. He needs access to Jira and Slack. But because he was added to the DevOps group for a quick fix, he inherited:
- Shadow Admin rights on AWS Production
- Write access to Customer Database
The Fix: Cydenti detects this toxic combination immediately. We visualize the path, quantify the impact, and recommend removing the redundant group membership while keeping his necessary app access.
Identity Security Posture-Built for SaaS and Cloud
Most tools focus on logs, infrastructure, or governance workflows. Cydenti focuses on the root problem: identity risk, where modern breaches begin.
Identity Security Posture Management
Automated configuration checks for M365, Salesforce & more.
Identity Threat Detection and Response
Detect active threats and anomalies in real-time.
Blast Radius
Visualize and reduce blast radius across multi-cloud.
Identity Risk Scoring
Quantify risk for every human and machine identity.
Integrates with your SaaS and cloud stack
API-based integrations across Microsoft 365, Google Workspace, Salesforce, AWS IAM, Azure AD, GCP IAM, GitHub, Slack, and ServiceNow. Deployed in minutes.
Real results, from day one
“Before Cydenti, we had no idea how many ghost identities existed in our SaaS stack. The platform discovered 47 unmanaged ones — including several from former contractors with active access for over a year.”
“Cydenti gave us visibility we never had. Within 48 hours, we discovered 12 orphaned accounts with admin rights, some belonging to employees who had left months ago.”
“We had no CISO and no budget for a full identity platform. Cydenti was operational in under 27 minutes and gave us our first risk report in less than 3 hours.”
Testimonials anonymized at clients’ request. Average deployment: 27 minutes.
Community & Gallery
Stay connected with our latest research, insights, and community discussions.
Frequently Asked Questions
Everything you need to know about Cydenti's SaaS Identity Security platform, from deployment to compliance.
Platform Overview
Discover your blind spots in 48 hours
— for free.
NIS2 enforcement begins October 1, 2026. The Audit Flash gives you a complete identity posture snapshot — service accounts, orphaned credentials, OAuth exposure — in 27 minutes. No commitment.
No commitment • No credit card • Data hosted in Europe • Response within 24h